
Parallels Remote
Application Server
Best Practices
Parallels International GmbH
Vordergasse 59
8200 Schaffhausen
Switzerland
Tel: + 41 52 672 20 30
www.parallels.com
Copyright © 1999-2019 Parallels International GmbH. All rights reserved.
This product is protected by United States and international copyright laws. The product’s underlying technology,
patents, and trademarks are listed at http://www.parallels.com/about/legal/.
Microsoft, Windows, Windows Server, Windows Vista are registered trademarks of Microsoft Corporation.
Apple, Mac, the Mac logo, OS X, macOS, iPad, iPhone, iPod touch are trademarks of Apple Inc., registered in the US
and other countries.
Linux is a registered trademark of Linus Torvalds.
All other marks and names mentioned herein may be trademarks of their respective owners.
Contents
Introduction ............................................................................................................... 5
Audience ........................................................................................................................... 5
Active Directory and Infrastructure Services Considerations .................................. 6
Active Directory ................................................................................................................. 6
DNS ................................................................................................................................ 10
DHCP ............................................................................................................................. 11
File Services .................................................................................................................... 11
Installation Procedures ........................................................................................... 14
Windows Server Requirements ....................................................................................... 14
Windows Server Roles & Features ................................................................................... 15
Remote Access Configuration ................................................................................ 18
Remote Desktop/Terminal Server Performance Settings ................................................. 18
General Performance Related Settings ............................................................................ 20
Configure RemoteFX ....................................................................................................... 21
General Purpose RemoteFX Settings .................................................................................... 22
RDP Optimizations .......................................................................................................... 35
For Windows 2008/R2 .......................................................................................................... 36
For Windows 2012/R2 .......................................................................................................... 36

Contents
RDP Security .................................................................................................................. 38
Locking Down TS/RDS Host ........................................................................................... 38
Disable Administrative Components ................................................................................ 40
Antivirus Exclusions ......................................................................................................... 42
Printer and Drive Mapping ...................................................................................... 44
Printer and Drive Mapping ............................................................................................... 44
Printing/Scanning Compression ...................................................................................... 45
Miscellaneous .......................................................................................................... 48
Load Balancing ............................................................................................................... 48
Groups ............................................................................................................................ 49
Filtering ........................................................................................................................... 50
Disable Application Monitoring ........................................................................................ 51
Server Reboots ............................................................................................................... 52
Backups ......................................................................................................................... 53
Large File Upload / Download via Drive Redirection ......................................................... 54
Remove Gateway Browsing from Your LAN .................................................................... 56
Remove Self-Signed Certificate Error .............................................................................. 57
Remote PCs ................................................................................................................... 60
VDI .................................................................................................................................. 61
Parallels RAS Web Portal ........................................................................................ 66
Windows Prerequisites for Parallels RAS Web Portal ....................................................... 66
Configure User Friendly URL ........................................................................................... 67
Parallels RAS HTML5 Gateway ............................................................................... 69
Index ........................................................................................................................ 70
Parallels Remote Application Server (RAS) is an application delivery and virtual desktop solution. It
extends Microsoft Windows Remote Desktop Services by providing centralized and simplified
management, universal printing and a highly available load balanced remote access solution to
Windows Terminal Services based applications and desktops from any device, anywhere. The
solution also includes a built-in Virtual Desktop Infrastructure (VDI) solution.
Traditionally, application delivery and VDI solutions were challenging to set up and manage. Design
and implementation could take weeks or even months to complete. In contrast, Parallels RAS can
be installed in days or even hours, providing a quicker return on your investment and an easier path
to realizing the benefits of remote desktop computing.
This document describes the best practice guidelines for deploying and configuring Parallels
Remote Application Server v15.x.
In This Chapter
Audience .................................................................................................................. 5
Audience
This guide is intended for system administrators responsible for installing and configuring Parallels
Remote Application Server. This guide assumes that the reader is already familiar with relevant
Microsoft services such as Active Directory, DNS, DHCP, Terminal Servers/Remote Desktop
Session Hosts and has an intermediate networking knowledge.
C HAPTER 1
Introduction

Parallels Remote Application Server can be installed in both Workgroup and Active Directory (AD)
environments where end users, RAS servers, and RDS servers belong to the same AD forest
(domains with single root domain) or multiple forests with trust relationships. Domains and
workgroups represent different methods for organizing computers in networks. The main difference
among them is how the computers and other resources on the networks are managed. For better
manageability and scalability, following Microsoft recommendations, Parallels recommends the use
of domains where:
• One or more computers are servers. Network administrators use servers to control security and
permissions for all computers in the domain. This makes it easy to make changes because they
are automatically made to all computers. Domain users must provide a password or other
credentials each time they access the domain.
• If you have a user account on the domain, you can log in to any computer in the domain
without needing an account on that computer.
• There can be thousands of computers in a domain.
• The computers can be on different local networks.
• File, folder, and user and group permissions can be assigned.
In This Chapter
Active Directory ......................................................................................................... 6
DNS .......................................................................................................................... 10
DHCP ....................................................................................................................... 11
File Services .............................................................................................................. 11
Active Directory
Parallels recommends for consideration the usage of the following Active Directory abilities.
Note: More information on Active Directory Domain Services can be found at
https://technet.microsoft.com/en-us/library/bb742424.aspx
C HAPTER 2
Active Directory and Infrastructure Services
Considerations

7
Active Directory and Infrastructure Services Considerations
Organization Units
A particularly useful type of directory object contained within domains is an organizational unit (OU).
OUs are Active Directory containers into which you can place users, groups, computers, and other
organizational units. An organizational unit cannot contain objects from other domains.
An OU can be used to assign Group policy settings for centralized management and configuration
of operating systems, applications, and user settings in an AD environment.
Parallels recommends the use of OUs for the following:
• Terminal Servers/Remote Desktop Session Hosts (RDSH) hosting applications and desktops
should be set in their own OUs. Usually TS/RDSH require various group policies applied to
them. For example, in a multi-user environment, policies may be required to optimize user
experience and/or add security.
Different OUs for different TS/RDSH groups identified from the Remote Application Server
Console can also be used to organize different application groups.
• Servers in the same Remote Application Server site should reside in the same domain or in
different domains with a full trust relationship between domains.
More information on Domain trusts can be found at https://technet.microsoft.com/en-
us/library/cc773178(v=ws.10).aspx

8
Active Directory and Infrastructure Services Considerations
• All servers that load-balance applications/desktops must be in the same domain if a domain
security group is authorized to use the application.
Note: For the information on how to design an OU structure which works for your organization, visit
https://technet.microsoft.com/en-us/library/2008.05.oudesign.aspx
Security Groups
Security groups are used to assign permissions to shared resources. Different resources (virtual
applications, desktops, VDI machines) can be assigned to different users/groups. Parallels
recommends the use of Active Directory Security groups for better manageability if filtering is done
via user/groups.
Once security groups are created in Active Directory and members are added to them, group-
based filtering can be carried out from the Remote Application Server Console. This will ensure that
all members of that particular security group will have access to same published resources. For
example, if a new user joins the company, they only need to be added to the Active Directory
security group to have access to given published resources.

9
Active Directory and Infrastructure Services Considerations
Examples of logical security group segregation can be based on the department user resides in or
based on application/desktop that is to be delivered.
More details about Active Directory Security Groups can be found at
https://technet.microsoft.com/en-us/library/dn579255(v=ws.11).aspx
Note: By default, in RAS published resources are available to all users in the domain if not restricted by
filtering (User/group, Client, IP Address, MAC or Gateway access).
Group Policies
Group Policy is an infrastructure that allows you to implement specific configurations for users and
computers. Group Policy settings are contained in Group Policy objects (GPOs), which are linked to
the following Active Directory service containers: sites, domains, organizational units (OUs). The
settings within GPOs are then evaluated by the affected targets using the hierarchical nature of
Active Directory. Consequently, Group Policy is one of the top reasons to deploy Active Directory
because it allows you to manage user and computer objects.
Apart from the Remote Application Server policies, which allow IT administrators to manage
Parallels Client policies for all users on the network who connect to a server in the farm, Parallels
recommends the additional use of group policies to manage different users and computer objects
accessing the infrastructure. Group policies relating to user experience and/or security are to be
linked with their respective OUs mentioned in the previous sections.
Some recommended group policies include but not limited to listed below.
Users Permissions
Logging in remotely requires users to have remote access rights to the remote server.
This can be carried out from Group Policy Management Console (GPMC), which is an
administrative feature that can be installed via Server Manager or through PowerShell as described
at https://technet.microsoft.com/en-us/library/cc725932(v=ws.11).aspx
Once GPMC is opened, navigate to Computer Configuration / Policies / Windows Settings /
Security Settings / Restricted Groups. Right-click on Restricted Groups and click on Add User
Group that should have access to log in on to the remote machine (TS/RDSH/VDI).
More information on how to add Domain Users/Group to the Remote Desktop Users group via
Group policy can be found at https://technet.microsoft.com/en-us/library/cc725932(v=ws.11).aspx

10
Active Directory and Infrastructure Services Considerations
Group Policy Loopback Processing
You can use the Group Policy Loopback feature to apply Group Policy objects that depend only on
which computer the user logs in to. This is ideal when users already reside in their respective OUs
and new OUs have been created to handle Terminal Server/RDSH from where the applications and
desktops are published. Essentially, we are applying user settings when they log in to those
computer objects, in this case to the Terminal Servers/RDSH.
This can be carried out from Group Policy Management Console (GPMC). Navigate to Computer
Configuration\Administrative Templates\System\Group Policy and then enable the Loopback
Policy option (Merge or Replace).
More information on loopback processing can be found at https://support.microsoft.com/en-
us/kb/231287
DNS
The Domain Name System (DNS) is a hierarchical distributed database that contains mappings of
DNS domain names to various types of data, such as IP addresses. DNS allows you to use friendly
names to easily locate computers and other resources on a TCP/IP network.
DNS is a key infrastructure component frequently used by various Remote Application Server
components. While standard file-based storage, such as the hosts file, will provide proper DNS
resolution in Proof of Concept (POC) environments, Parallels recommends implementing Active
Directory integrated DNS in enterprise deployments.
Parallels recommends the use of the DNS zone integrated with Active Directory so that
organizations can have the benefit of using secure dynamic updates, as well as the ability to use
Access Control List (ACL) editing features to control which machines can update the DNS system.
Dynamic updates are a key feature of DNS, which allows domain computers to register their name
and IP addresses with the DNS server automatically when they come online or change IP
addresses through the DHCP server. The DNS Server service allows dynamic update to be enabled
or disabled on a per-zone basis on each server that is configured to load either a standard primary
or directory-integrated zone. By default, the DNS Client service dynamically updates host (A)
resource records in DNS when the service is configured for TCP/IP. This form of update eliminates
the need for manual entries of names and IP addresses into the DNS database.
There is a security concern when automatic update from a client to the DNS database could take
place and thus create the possibly for a malicious entry. Therefore, secure dynamic updates will
verify that the computer that is requesting the update to the DNS server also has an entry in the
Active Directory database. This means that only computers that have joined the Active Directory
domain can dynamically update the DNS database.
More information on how DNS works can be found at
https://technet.microsoft.com/library/cc772774.aspx

11
Active Directory and Infrastructure Services Considerations
Reverse Lookup
In most Domain Name System (DNS) lookups, clients typically perform a forward lookup, which is a
search based on the DNS name of another computer as it is stored in a host (A) resource record.
This type of query expects an IP address as the resource data for the answered response.
DNS also provides a reverse lookup process in which clients use a known IP address and look up a
computer name based on its address.
DHCP
Dynamic Host Configuration Protocol (DHCP) is a client/server protocol that automatically provides
an Internet Protocol (IP) host with its IP address and other related configuration information such as
the subnet mask and default gateway.
Parallels recommends the use of static or DHCP reserved IP addressing for Remote Application
Server infrastructure servers.
With regards to VDI, to create a RAS template from an existing virtual guest, the guest operating
system (Windows) must be configured to obtain an IP address via the DHCP server. With regards
to a VDI agent on hypervisors it is recommended to take note of the MAC address assigned to the
appliance and add a DHCP reservation. If DHCP isn't available, a static IP address needs to be
configured manually.
For Wyse clients, RAS Secure Client Gateway can act as a Wyse broker. Please ensure that DHCP
option 188 on your DHCP server is set to the IP Address of this Gateway for thin clients that are
going to boot via this gateway.
Note: Parallels Remote Application Server should not to be installed on a domain controller or any other
server where a DHCP server is running.
File Services
For a consistent visual display of personal data associated with a specific user and/or a customized
desktop environment irrespective to which TS/RDSH or VDI machine user is connecting, Parallels
recommends the use of Microsoft roaming profiles and folder redirection or User Profile Disks for a
complete profile management solution with Remote Application Server.
The following requirements are important to be noted prior the profile solution implementation:
• When deploying Roaming User Profiles with Folder Redirection in an environment with existing
local user profiles, deploy Folder Redirection before Roaming User Profiles to minimize the size
of roaming profiles. After the existing user folders have been successfully redirected, you can
deploy Roaming User Profiles.

12
Active Directory and Infrastructure Services Considerations
• To administer Roaming User Profiles or User Profile Disks, you must be signed in as a member
of the Domain Administrators security group, the Enterprise Administrators security group, or
the Group Policy Creator Owners security group.
• Client computers must run Windows 8.1, Windows 8, Windows 7, Windows Vista,
Windows XP, Windows Server 2016, Windows Server 2012 R2, Windows Server 2012,
Windows Server 2008 R2, Windows Server 2008, or Windows Server 2003. Note that
Windows XP and Windows Server 2003 support Roaming User Profiles only when set up on
user accounts and not on a per-computer basis by using Group Policy.
• Client computers must be joined to the Active Directory Domain Services (AD DS) that you are
managing.
• A file server must be available to host roaming user profiles or User Profile Disks.
• If the file share uses DFS Namespaces, the DFS folders (links) must have a single target to
prevent users from making conflicting edits on different servers.
• If the file share uses DFS Replication to replicate the contents with another server, users must
be able to access only the source server to prevent users from making conflicting edits on
different servers.
• If the file share is clustered, disable continuous availability on the file share to avoid performance
issues

13
Active Directory and Infrastructure Services Considerations
More information on deploying users profiles can be found at https://technet.microsoft.com/en-
us/library/jj649079.aspx. And about User Profile Disks
https://blogs.technet.microsoft.com/enterprisemobility/2012/11/13/easier-user-data-management-
with-user-profile-disks-in-windows-server-2012.
For a high availability profile management solution and for scalability requirements, Parallels
recommends the use of Microsoft DFS and DFSR to host the namespace and handle the
replication between target file servers respectively. More information on DFS and DFSR can be
found at https://technet.microsoft.com/en-us/library/jj127250.aspx
In This Chapter
Windows Server Requirements ................................................................................. 14
Windows Server Roles & Features ............................................................................ 15
Windows Server Requirements
All Parallels RAS farm server components are Windows Server based, with the exception of the
HALB and VDI virtual appliances.
Supported Windows platforms:
• Windows Server 2003 SP1 (Terminal Server Agent only)
• Windows Server 2008
• Windows Server 2008 R2
• Windows Server 2012
• Windows 2012 R2
• Windows Server 2016
Active Directory
Parallels RAS can be installed using Active Directory or Local Windows Security.
• VDI for RAS requires Active Directory.
• Installation of any RAS component on an Active Directory Domain Controller is not supported.
If using Active Directory, Windows Servers must be joined to a Domain and the right hostname
configured before installing RAS.
• Do not change the server hostname after installing Parallels RAS or reconfiguration of Parallels
RAS would be required.
Networking Requirements
Use a static or permanently reserved DHCP address.
C HAPTER 3
Installation Procedures

15
Installation Procedures
SSL on the Gateway servers requires name resolution. For Gateways to function properly, one of
the two following conditions must be met:
• DNS resolution must be available.
• HOSTS files can be configured for DNS resolution.
See the Active Directory and Infrastructure Services Considerations chapter (p. 6).
Windows Firewall Requirements
RAS v15 and higher can automatically configure Windows Firewall settings during installation or
deployment of additional RAS farm components to allow communication between different RAS
Servers in a farm.
• For manual configuration of the Windows Firewall, do not check the "Add Firewall Rules" when
deploying RAS components.
• A comprehensive list of required Firewall ports can be found in the Port Reference section of
the Parallels Remote Application Server Administrator’s Guide, which can be download from
http://www.parallels.com/products/ras/resources/.
When pushing RAS components to another server from the RAS console, one of the following
conditions must be met on the remote server:
• Open Windows Firewall ports TCP 135, 445, 49179, then push the RAS components and have
the Windows Firewall ports automatically configured.
• Temporarily disable Windows Firewall, push the RAS components and have RAS automatically
configure the firewall settings, and then re-enable the Windows Firewall.
• Manually configure Windows Firewall settings as described in the Port Reference section of the
Parallels Remote Application Server Administrator's Guide, and then install the RAS
component(s).
Windows Server Roles & Features
In order to install Parallels RAS on Windows servers, there are some required prerequisite to be
installed from the Server Roles and Features.
• The Publishing Agent Server can be installed on any supported version of Windows. The
Publishing Agent does not require any specific Windows roles or features.
• The Secure Client Gateway can be installed on any supported version of Windows. The Secure
Client Gateway does not require any specific Windows roles or features.
• The Terminal Server agent requires the following roles installed:
• Terminal Server Role for Windows Server versions 2003 SP1 up till 2008.

16
Installation Procedures
• Remote Desktop Session Host for Windows Server versions 2008 R2 up to 2016.
• For v15 and later, the Remote Desktop Session Host role can be automatically installed
using the "Add Terminal Server" capability from the RAS Console.
Parallels RAS does not replace the need for Microsoft Client Access Licenses (CALs). A Windows
Remote Desktop/Terminal Server License server is required.
Except for very small, single-server environments, the License Server should not be installed on the
production Terminal Servers or Remote Desktop Session Hosts.
More information on TS/RDS CALs can be found at https://technet.microsoft.com/en-
us/library/cc753650(v=ws.11).aspx
Ensure that Desktop Experience is installed on all Terminal Servers
When a user connects a Parallels RAS server, the desktop that exists on the RD Session Host
server is reproduced in the remote session by default. To make the remote session look and feel
more like the user's local Windows desktop, install the Desktop Experience feature on an RD
Session Host server that is running Windows Server 2008 R2, Windows 2012 , Windows 2012 R2.
Note that Windows 2016 has the Desktop Experience feature enabled by default on RDS host. This
also makes the graphics look better using the Windows Aero theme.
Desktop Experience is a feature that you can install from Server Manager.

17
Installation Procedures
Once Desktop Experience is enabled, you will notice that applications display richer graphics and a
remote desktop looks more like the client's local desktop with themes and other Windows client
components.
In This Chapter
Remote Desktop/Terminal Server Performance Settings........................................... 18
General Performance Related Settings ..................................................................... 20
Configure RemoteFX ................................................................................................ 21
RDP Optimizations ................................................................................................... 35
RDP Security ............................................................................................................ 38
Locking Down TS/RDS Host .................................................................................... 38
Disable Administrative Components ......................................................................... 40
Antivirus Exclusions .................................................................................................. 42
Remote Desktop/Terminal Server Performance
Settings
The default Windows performance settings are intended for general purpose servers. In order to
maximize application or desktop hosting server performance, the default Windows performance
settings should be adjusted on Windows Remote Desktop/Terminal Servers.
From the Control Panel go to System and click on Advanced System Settings. Under the
Advanced tab in the System Properties dialog box, click on Settings under the Performance
section.
Performance Options settings
Under the Visual Effects tab from the Performance Options dialog box, change the setting to
Adjust for best performance.
C HAPTER 4
Remote Access Configuration

19
Remote Access Configuration
If a specific application has a custom setting recommendation, you should use it, but in general, the
Adjust for best performance option will provide the best overall performance in a Parallels RAS
environment.
Windows paging file settings
Set the Windows paging file to twice the amount of RAM. For heavier workloads, a paging file of
three times the amount of physical memory might be required. For more information on how to
determine the exact page file size, please visit https://support.microsoft.com/en-
us/help/2860880/how-to-determine-the-appropriate-page-file-size-for-64-bit-versions-of-windows
By default, Microsoft Windows page file size is automatically managed for all drives and grows
dynamically as necessary. However, as the system ramps up to intended capacity, dynamic page
file growth can result in a fragmented page file, so it is best to set a fixed page file size upfront.
Typically, page file settings are configured when the server is first installed. However, if the server
remained in production for a while, Parallels recommends optimizing and defragmenting the drive
prior to setting paging options described below.
Note: If the size of the page file is too small, system will generate a mini dump and will log an event in the
System event log during boot to inform you about this condition.

20
Remote Access Configuration
In the example below. the server has 8 GB of RAM:
Note that Microsoft sets it to 1280 but recommends 4607. Parallels recommends to double it and
use a new page file on the disk. Therefore the number is 16384 (8 GB in block of 8192 x2 =
16384). Make sure you have enough free disk space to use this setting.
General Performance Related Settings
Whether you are using graphics intensive applications or streaming media across RDP, some
configurations can be applied to provide performance benefits in your environment:
• Display driver optimization – this is probably the most important component, particularly on the
Windows CE platforms that tend to have a lot less CPU power than their desktop
counterparts. The display "device driver interface" we provide in Windows CE uses only the
basic graphics engine functions; where software acceleration is provided through emulation
libraries, and hardware acceleration is limited to two-dimensional graphics operations. If at all
possible, hardware acceleration should be used.

21
Remote Access Configuration
• Ensure that your video and network card drivers are up to date based on the manufacturer’s
recommendations.
• Enable bitmap caching in your RDP session. This can result in some significant bandwidth
savings and can also improve the refresh speed. However, this does not mean that graphics
intensive applications will run at the same performance level as they would in a non-RDP
session.
• Understanding how font exchange works can also lead to some opportunities for performance
improvements. Font exchanges occur between the client and server to determine which
common system fonts are installed. The client notifies the Terminal Server of all installed
system fonts to enable faster text rendering during an RDP session. When the Terminal Server
knows what fonts the client has available, passing compressed fonts and Unicode character
strings rather than larger bitmaps to the client can save network bandwidth
• If network bandwidth is not as much of a concern, you can increase the frame rate on the client
side via a registry modification.
https://blogs.technet.microsoft.com/askperf/2009/04/17/terminal-services-and-graphically-
intensive-applications/
To learn how to increase the frame rate on the server side, see https://support.microsoft.com/en-
us/help/2885213/frame-rate-is-limited-to-30-fps-in-windows-8-and-windows-server-2012-remote-
sessions.
Configure RemoteFX
RemoteFX is a set of Microsoft Windows technologies that greatly enhances the end-user visual
and performance experience over the RDP protocol. It is available in Windows Server 2008 R2
SP1 and later. Windows 7 was the first client side operating system to support RemoteFX. Both
the client and the server versions must be able to support RemoteFX in order for these
enhancements to work.
Although RAS supports earlier versions of Windows Server, certain performance capabilities will not
be available when those versions are used. RemoteFX has been improved with subsequent
releases of Windows. The best performance will always occur when running the latest version of
Microsoft Windows Server being accessed from the latest workstation version. Older versions of
Windows can connect with newer versions (e.g.: Windows XP to Windows 2012 R2 or Windows 10
to Windows 2003) and while this might be acceptable for certain workloads, RemoteFX capabilities
will not be available.
Parallels RAS supports RemoteFX on the following clients:
• Parallels Windows Client for Windows installed on Windows 7 SP1 and higher.
• Parallels Client for Mac
• Parallels Client for Linux
• Parallels Client for iOS

22
Remote Access Configuration
• Parallels Client for Android
• Parallels Client for ChromeApp running on ChromeBooks
General Purpose RemoteFX Settings
RemoteFX is enabled on Windows systems using Group Policy. Parallels recommends to apply
Group policies at OU (organizational unit) level in Active Directory environments. Although local
Group Policies can be used, it requires to configure necessary settings on every Terminal
Server/Remote PC/VDI Guest in the RAS farm.
Hint: To edit domain Group Policies, from the Windows Run command, type GPMC.MSC. Once the
Group Policy settings are completed, run GPUPDATE /FORCE from the Run command to apply them.
Remote FX Settings for Server 2008 R2
Enable the following options on all Terminal Servers in your farm. Under Computer
Configuration\Administrative Templates\Windows Components\Remote Desktop Services\Remote
Desktop Session Host\Remote Session Environment enable the following:
• Configure RemoteFX
• Optimize visual experience when using RemoteFX. Set to Medium Default.
• Set Compression algorithm for RDP data. Set to Optimize to use less network bandwidth.
• Optimize Visual experience for Remote Desktop Services sessions. Set to Rich Multimedia.
• Configure image quality for RemoteFX Adaptive Graphics (Image Quality set to Medium).
• Configure RemoteFX Adaptive Graphics. Set to Let the system choose experience for network
conditions.

23
Remote Access Configuration
RemoteFX settings for Server 2012 and 2012 R2
Enable the following options on all Terminal Servers in your farm. Under Computer
Configuration\Administrative Templates\Windows Components\Remote Desktop Services\Remote
Desktop Session Host\Remote Session Environment enable the following:
• Configure Compression for RemoteFX Data. Set to Optimize to use less network bandwidth.
• Configure image quality for RemoteFX Adaptive Graphics. Set to Medium.
• Enable RemoteFX encoding for RemoteFX clients designed for Windows Server 2008 R2 SP1
• Configure RemoteFX Adaptive Graphics. Set to Let the system choose the experience for
network conditions.
RemoteFX Settings for Windows Workstations Running Remote PC
Agents and Guest Agents
Remote FX Settings for Windows 7 SP1. Under Computer Configuration\Administrative
Templates\Windows Components\Remote Desktop Services\Remote Desktop Session
Host\Remote Session Environment enable the following options for virtual PC or VDI desktop which
has guest agent installed:
• Enable RemoteFX.
• Set Compression algorithm for RDP data. Set to Optimize to use less network bandwidth.
• Optimize Visual experience for Remote Desktop Services sessions. Set to Rich Multimedia.
• Configure compression for RemoteFX data. Set to Optimize to use less network bandwidth.
• Configure image quality for RemoteFX Adaptive Graphics. Set to Medium.
• Configure RemoteFX Adaptive Graphics. Set to Let the system choose the experience for the
network condition.

24
Remote Access Configuration
Configure RemoteFX Adaptive Graphics
RemoteFX supports two Group Policy settings that give administrators the flexibility to manually
choose the best configuration for their scenario. Both policies are under this path: Computer
Configuration\Administrative Templates\Windows Components\Remote Desktop Services\Remote
Desktop Session Host\Remote Session Environment.
The first policy setting is Configure image quality for RemoteFX Adaptive Graphics. This policy
setting specifies the graphics quality for a remote session. Administrators can use this option to
balance network bandwidth usage with graphics quality delivered.
The options are Medium (default), High, and Lossless. The Medium setting consumes the lowest
amount of bandwidth, The High setting increases the image quality with a moderate increase in
bandwidth consumption, while the Lossless setting uses lossless encoding, which preserves full
color and resolution integrity but requires significant increase in bandwidth.
The second policy setting is Configure RemoteFX Adaptive Graphics. This policy setting allows
the administrator to choose the encoding configuration to be optimized for server scalability or
bandwidth usage. If you enable this policy setting, the RemoteFX experience could be set to one of
the following options:
• Let the system choose the experience for the network condition
• Optimize for experience (balanced)
• Optimize to use minimum network bandwidth
By default, the system will choose the best experience based on available network bandwidth.
Configure RemoteFX Lossless Graphics
This policy setting allows the administrator to configure RemoteFX graphics for Remote Desktop
Session Host or Remote Desktop Virtualization Host servers to be lossless. If you enable this policy
setting, RemoteFX graphics will use lossless encoding. The color integrity of the graphics data will
stay intact. If you disable or skip the configuration of this policy setting, RemoteFX graphics lossless
encoding will be disabled.
Use the Hardware Default Graphics Adapter for all Remote Desktop
Services Sessions
This policy setting enables system administrators to change the graphics rendering for all Remote
Desktop Services sessions on a Remote Desktop Session Host (RD Session Host) server. If you
enable this policy setting, all Remote Desktop Services sessions on the RD Session Host server
use the hardware graphics renderer instead of the Microsoft Basic Render Driver as the default
adapter. If you disable or skip the configuration of this policy setting, all Remote Desktop Services
sessions on the RD Session Host server will use the Microsoft Basic Render Driver as the default
adapter.

25
Remote Access Configuration
Note: The policy setting affects only the default graphics processing unit (GPU) on a computer with more
than one GPU installed. All additional GPUs are considered secondary adapters and used as hardware
renderers. The GPU configuration of the local session is not affected by this policy settings.

26
Remote Access Configuration
Remote FX USB Redirection
In order to get Point of Sale / USB Scanning devices to work properly with Windows 2008 R2 and
higher, you must enable RemoteFX USB redirection on the user Windows devices using GPO.
Please note that this policy setting allows you to permit RDP redirection of other supported
RemoteFX USB devices from this computer. Make sure that you set RemoteFX USB Redirection
Access Rights to Administrators and Users. This is configured by navigating to Computer
Configurations > Administrative Templates > Windows Components > Remote Desktop Services >
Remote Desktop Session Host > Remote Desktop Connection Client:

27
Remote Access Configuration
Enable Audio / Recording Redirection
In order to allow audio playback and recording redirection, first enable and start “Windows Audio
Service” in the Services.msc console and enable server’s playback device, and then enable these
functions using group policy. Terminal Servers do not need a sound card to do this.

28
Remote Access Configuration
To enable the sound option on all Terminal Servers, right-click the server’s sound icon in the
Windows system tray. You will then be prompted to enable remote audio.
To enable the sound redirection options, navigate to Computer Configurations > Administrative
Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host
> Remote Desktop Session Host > Device and Resource Redirection and select the following
options:
• Allow audio and video playback redirection
• Allow audio recording redirection

29
Remote Access Configuration
• Limit audio playback quality

30
Remote Access Configuration
Audio and Video Playback
Audio and video playback allows users to redirect the remote computer audio in a remote session.
It provides an improved experience for video playback in remote sessions. By default, audio and
video playback is not allowed when connecting to a computer running Windows Server 2008 R2.
https://technet.microsoft.com/en-us/library/dd759165.aspx
Audio and video playback redirection is allowed by default when connecting to a computer running
Windows 8, Windows Server 2012 R2, Windows 7, Windows Vista, or Windows XP Professional.
Time Zone Redirection
If you have users that login from different time zones, you may want to enable this setting. This
setting will redirect the local time to the app, remote PC, or VM. Time Zone Redirection is
configured in the same Group Policy location as Audio Redirection: Local Computer Policy >
Computer Configurations > Administrative Templates > Windows Components > Remote Desktop
Services > Remote Desktop Session Host > Remote Desktop Session Host > Device and
Resource Redirection.

31
Remote Access Configuration
Device and Resource Redirection
Generally, device redirection increases how much network bandwidth RD Session Host server
connections use because data is exchanged between devices on the client computers and
processes that are running in the server session. The extent of the increase is a function of the
frequency of operations that are performed by the applications that are running on the server
against the redirected devices. Printer redirection and Plug and Play device redirection also
increases CPU usage at sign-in.
Parallels recommends to not allow device redirection if not being used since this will result in
inefficient bandwidth usage. Local device redirection can be configured from Parallels Remote
Application Server policies, registry, or Microsoft group policies.

32
Remote Access Configuration
Remote Session Environment (H.264, RemoteFX, Adaptive Acceleration)

33
Remote Access Configuration
Set the Configure image quality for RemoteFX Adaptive Graphics option to Medium:

34
Remote Access Configuration
Windows 2008 R2 RemoteFX Compatibility

35
Remote Access Configuration
RDP Optimizations
Microsoft Windows Server 2008 R2 and later include bulk compressors that compress all data sent
from the server to the client. These are available in addition to the bulk compressor present in RDP
5.0 (in Windows 2003). These compressors can be enforced by the computer-wide Set
compression algorithm for RDP data Group Policy setting.
The choice of compression algorithm impacts the memory and CPU consumption on the server
and thus affects server scalability. RDP optimization can be configured to:

36
Remote Access Configuration
• Use the least amount of memory
• Use the least amount of network bandwidth
• Balance between memory and network bandwidth utilization (default)
For Windows 2008/R2
Navigate to Computer Configuration\Administrative Templates\Windows Components\Terminal
Services\Terminal Server\Remote Session Environment and set compression algorithm for RDP
data as follows:
Optimized to use less memory (RDP 5.2 or V1):
• Bulk compressor from Windows Server 2003
• Consumes more bandwidth than other compressors
• Has the least memory and CPU overhead
• Gives you the best server-side scalability
Balances network bandwidth and memory (RDP 6.0 or V2):
• The default setting if the Group Policy setting is not configured
• Balances between memory consumption and network bandwidth
• Can reduce your bandwidth by 5–30 percent compared to the RDP 5.2 compressor
Optimized to use less network bandwidth (RDP 6.1 or V3):
• A new compressor designed for Windows Server 2008
• Tuned to give you the best network performance
• Can reduce your bandwidth by 10–60 percent compared to the RDP 5.2 compressor
http://download.microsoft.com/download/4/d/9/4d9ae285-3431-4335-a86e-
969e7a146d1b/RDP_Performance_WhitePaper.docx
For Windows 2012/R2
Navigate to Computer Configuration\Administrative Templates \Windows Components\Remote
Desktop Services \ Remote Desktop Session Host\ Remote Session Environment and configure
compression for RemoteFX data as follows:
• Optimized to use less memory. Consumes the least amount of memory per session but has
the lowest compression ratio and therefore the highest bandwidth consumption.
• Balances memory and network bandwidth. Reduced bandwidth consumption while
marginally increasing memory consumption (approximately 200 KB per session).

37
Remote Access Configuration
• Optimized to use less network bandwidth. Further reduces network bandwidth usage at a
cost of approximately 2 MB per session. If you want to use this setting, you should assess the
maximum number of sessions and test to that level with this setting before you place the server
in production.
You can also choose not to engage a RemoteFX compression algorithm. This will use more
network bandwidth and it is only recommended if you are using a hardware device that is designed
to optimize network traffic. Even if you choose not to use a RemoteFX compression algorithm,
some graphics data will still be compressed.
https://msdn.microsoft.com/en-us/library/windows/hardware/dn567648(v=vs.85).aspx
The following policy setting specifies whether the Remote Desktop Protocol will try to detect the
network quality (bandwidth and latency): Computer Configuration\Administrative
Templates\Windows Components\Remote Desktop Services\Remote Desktop Session
Host\Connections\Select network detection on the server.
If you enable the above policy setting, you must select one of the following:
• Connect Time Network Detect
• Continuous Network Detect
• Connect Time Detect
• Continuous Network Detect
If you select Connect Time Network Detect, Remote Desktop Protocol will not try to determine the
network quality at the connect time, and it will assume all traffic to this server originates from a low
speed connection.
If you select Continuous Network Detect, Remote Desktop Protocol will not try to adopt to
changing network quality.
If you select Connect Time Detect and Continuous Network Detect, Remote Desktop Protocol will
not try to determine the network quality at the connect time, it will assume all traffic to this server
originates from a low speed connection and it will not try to adopt to changing network quality.
If you disable or do not configure this policy setting, Remote Desktop Protocol will spend a few
seconds trying to determine the network quality prior to the connection and it will continuously try
to adopt to the network quality.
The following policy setting specifies whether the UDP protocol will be used for Remote Desktop
Protocol access to this server: “Computer Configuration\Administrative Templates \Windows
Components\Remote Desktop Services \ Remote Desktop Session Host\ Connections\Select RDP
transport protocols".
If you enable the above policy setting, Remote Desktop Protocol traffic to this server will only use
the TCP protocol. If you disable or do not configure this policy setting, Remote Desktop Protocol
traffic to this server will use both the TCP and UDP protocols.

38
Remote Access Configuration
RDP Security
Locking Down TS/RDS Host
Server Manager Console
Disable Server Manager Pop up for users logging in. This can be done from the Group Policy
Microsoft Management Console (MMC):
User Configuration \ Polices \ Administrative Templates \ Start Menu and Taskbar
Some administrative group polices might not be available in the Group Policy Manager Console
(GPMC). These can be imported from https://www.microsoft.com/en-
au/download/details.aspx?id=41193

39
Remote Access Configuration
Removing Favorites and Libraries
You must perform these modifications on the RD Session Host servers. You can use the Registry
to make these changes directly or using group policy preferences (GPP).
Note: Back up the key first and take ownership of the ShellFolder before changing the value of
Attributes.
• For Favorites, the key is:
[HKEY_CLASSES_ROOTCLSID{323CA680-C24D-4099-B94D-446DD2D7249E}ShellFolder]
"Attributes"=dword:a0900100
Changing a0900100 to a9400100 will hide Favorites from the navigation pane.
• For Libraries, the key is:
[HKEY_CLASSES_ROOTCLSID{031E4825-7B94-4dc3-B131-E946B44C8DD5}ShellFolder]
"Attributes"=dword:b080010d
Changing b080010d to b090010d will hide Libraries from the navigation pane.
Hiding/Preventing Access to Drives and other features
You can use Group Policy settings to hide and restrict access to drives on the RD Session Host
server. By enabling these settings you can ensure that users do not inadvertently access data
stored on other drives, or delete or damage programs or other critical system files on drive C.
This can be carried out from the Group Policy Microsoft Management Console (MMC) as follows:
• For Windows 2008\R2: User Configuration\Policies\Administrative Templates\Windows
Components\Windows Explorer.
• For Windows 2012\R2: User Configuration/ Administrative Templates/ Windows Components/
File Explorer.
Additional policies can be set to:
• Hide the Manage item on the Windows Explorer context menu
• Remove Hardware tab
• Remove "Map Network Drive" and "Disconnect Network Drive"
• Remove Search button from Windows Explorer
• Disable Windows Explorer’s default context menu
• Remove Run menu from Start Menu
https://blogs.msdn.microsoft.com/rds/2011/05/26/how-to-restrict-users-from-accessing-local-
drives-of-an-rd-session-host-server-while-using-remoteapp-programs/

40
Remote Access Configuration
Session Limits
You can use this policy setting to specify the maximum amount of time that an active,
disconnected, or idle session remains in its current state.
Set the time limit for disconnected sessions. When a session is disconnected, running programs
are kept active even though the user is no longer actively connected. By default, these
disconnected sessions are maintained for an unlimited time on the server.
Set the time limit for logoff of published resources sessions. You can specify how long a user
session will remain in a disconnected state after closing all programs but before the session is
logged off from the RD Session Host server. By default, if a user closes a published resource, the
session is disconnected from the RD Session Host server but it is not logged off.
This option can also be changed in the Parallels RAS Console by navigating to Farm \ Terminal
Servers \ Properties \ Publishing Session.
Set time limit for logoff of published resources sessions. When a user closes the last running
published resource associated with a session, Remote Application Server will keep the session in a
disconnected state until the specified time limit is reached. When it is, the session will be logged off
from the RD Session Host server. If the user starts another published resource before the time limit
is reached, the user will reconnect to the disconnected session on the RD Session Host server.
Note: This policy setting appears in both Computer Configuration and User Configuration. If both policy
settings are configured, the Computer Configuration policy setting takes precedence. These
configurations can be carried out from the Group Policy Microsoft Management Console (MMC):
Computer Configuration\Policies\Administrative Templates\Windows Components\Remote Desktop
Services\Remote Desktop Session Host\Session Time Limits.
Disable Administrative Components
Disable Control panel items, Administrative Tools, and PowerShell
Various control panels, administrative tools, and server settings should be disabled for standard
user access if otherwise not required by organization. To disable control panel items, the following
policies can be carried out from the Group Policy Microsoft Management Console (MMC): User
Configuration\Administrative Templates\Control Panel
Disable Registry Modification
For added security, users should be restricted to not make any registry modifications: User
Configuration\Policies\Administrative Templates\System

41
Remote Access Configuration
Windows Updates and Installer
These policy setting prevents users from using Windows Installer to install patches and disables
Windows update and shutdown notifications. This can be carried out from the Group Policy
Microsoft Management Console (MMC):
• Computer Configuration\Policies\Administrative Templates\Windows Components\Windows
Installer
• Computer Configuration\Administrative Templates\Windows Components\Windows Update
Control Panel
The following Control Panel items may be removed from the list of items available for standard user
access:
• Microsoft.AdministrativeTools
• Microsoft.AutoPlay
• Microsoft.ActionCenter
• Microsoft.ColorManagement
• Microsoft.DefaultPrograms
• Microsoft.DeviceManager
• Microsoft.EaseOfAccessCenter
• Microsoft.FolderOptions
• Microsoft.iSCSIInitiator
• Microsoft.NetworkAndSharingCenter
• Microsoft.NotificationAreaIcons
• Microsoft.PhoneAndModem
• Microsoft.PowerOptions
• Microsoft.ProgramsAndFeatures
• Microsoft.System
• Microsoft.TextToSpeech
• Microsoft.UserAccounts
• Microsoft.WindowsFirewall
• Microsoft.WindowsUpdate
• Microsoft.DateAndTime
• Microsoft.RegionAndLanguage
• Microsoft.RemoteAppAndDesktopConnections

42
Remote Access Configuration
• Install Application On Remote Desktop Server
• Java
• Flash Player
Administrative Tools and PowerShell
• Navigate to Computer Configuration > Policies > Windows Settings > Security Settings.
• Right click on File System, choose Add File.
• In the Add a file or folder window, put %AllUsersProfile%\Microsoft\Windows\Start
Menu\Programs\Administrative Tools in the Folder field and click OK.
• On the next window Database Security for%AllUsersProfile%\Microsoft\Windows\Start
Menu\Programs\Administrative Tools\Server Manager.lnk remove Users and check that
Administrators have Full Access
• On the Add Object window choose Configure this file or folder then Propagate inheritable
permissions to all subfolders and files. Click OK.
• Do the same for PowerShell shortcut (+ delete Creator Owner in database
security): %AllUsersProfile%\Microsoft\Windows\Start Menu\Programs\System Tools\Windows
PowerShell.lnk
• Do the same for Server Manager shortcut: %AllUsersProfile%\Microsoft\Windows\Start
Menu\Programs\Administrative Tools\Server Manager.lnk
Antivirus Exclusions
Installing antivirus software on an RD Session Host server greatly affects overall system
performance, especially the CPU usage. We highly recommend that you exclude all folders that
hold temporary files from the active monitoring list, especially folders generated by services and
other system components.
The Parallels RAS folder to be excluded from real-time scanning is
%programfiles(x86)%\Parallels\ApplicationServer.
For Parallels RAS port reference, please refer to Parallels Remote Application Server
Administrator's Guide, which can be downloaded from
http://www.parallels.com/products/ras/resources. For additional information, please also see
http://kb.parallels.com/124003.
The Parallels Client for Windows folder to be excluded from real-time scanning is as follows:
• 32-bit: %programfiles(x86)%\Parallels\Client
• 64-bit: %programfiles%\Parallels\Client

43
Remote Access Configuration
Parallels recommends to exclude the above Parallels RAS and Parallels Client for Windows folders
from real-time or on-access scanning and scan them on a regular basis using scheduled scans.
You should also monitor the creation of new files in the excluded folders.

In This Chapter
Printer and Drive Mapping ........................................................................................ 44
Printing/Scanning Compression ............................................................................... 45
Printer and Drive Mapping
When publishing applications, sometimes the applications will open faster than GPO’s, logon
scripts, profiles or printer mapping can complete. To resolve this, Parallels RAS has the capability
to introduce a delay which allows these processes to complete before launching the application.
Beginning with RAS v15 the default setting is 20 second delay. The default can be changed and
the delay can be adjusted on a per application basis.
You can see from the example below that the Inherit default setting option is set for all
applications to wait until RAS Universal Printers are redirected.
This option only works on Published applications from RDS/TS servers, Remote PC published
applications and VDI published applications. It does not affect full desktop publishing as this type of
remote access utilizes the standard Windows logon process.
To configure the Application Delay Settings:
1 In the RAS console, navigate to Publishing.
2 Click on a desired published application.
3 Click on the Display tab.
C HAPTER 5
Printer and Drive Mapping

45
Printer and Drive Mapping
4 For individual applications, select the Wait until all RAS Universal Printers are redirected
before showing the application option.
5 This option will also force drive mapping with an application.
6 If you have an application that must utilize a mapped network drive, this option will insure that
the drive is mapped prior to running the application.
7 When the printers are properly mapped, they will appear on the client side as
"%PRINTERNAME% for %USERNAME% by Parallels".
Printing/Scanning Compression
For Windows desktop clients (full and basic), Parallels RAS v15.5 and higher includes Universal
printing compression policy and Universal scanning compression policy options. These
options allow system administrator to adjust printing and scanning compression levels via client
policy settings in the RAS Console.
To set printing and scanning compression policies:
1 In the RAS Console, select the Policies category.
2 Right-click an existing policy and choose Properties.

46
Printer and Drive Mapping
3 In the Policy Properties dialog, click Connection Properties in the left pane and then click the
Experience tab in the right pane.
4 Select one of the following options from the Universal printing compression policy or
Universal scanning compression policy drop-down lists:
• Compression disabled
• Best speed (uses less CPU)
• Best size (uses less network traffic)
• Based on connection speed (default)
If the type of printed or scanned documents is predictable — for instance, your documents are
always very small or always very large — you can benefit by selecting an appropriate compression
policy. However, compression brings the most benefit to network connections with limited
bandwidth or latency when printing or scanning often slows down thus negatively affecting user
experience.

47
Printer and Drive Mapping
Parallels recommends using the Best size compression policy to make printing/scanning jobs
smaller and transfer them faster if the client devices are powerful enough from the CPU and
memory perspective. If the client devices are not powerful enough, the Best speed option policy
should be used.
For more info, please also see the Parallels Remote Application Server Universal Printing Best
Practices Guide, which can be downloaded from
http://www.parallels.com/products/ras/resources/.

In This Chapter
Load Balancing ........................................................................................................ 48
Groups ..................................................................................................................... 49
Filtering .................................................................................................................... 50
Disable Application Monitoring .................................................................................. 51
Server Reboots ........................................................................................................ 52
Backups ................................................................................................................... 53
Large File Upload / Download via Drive Redirection .................................................. 54
Remove Gateway Browsing from Your LAN ............................................................. 56
Remove Self-Signed Certificate Error ........................................................................ 57
Remote PCs ............................................................................................................. 60
VDI ........................................................................................................................... 61
Load Balancing
By default, the Resource Based load balancing is enabled. It is recommended that this setting is
remained as is for better resource utilization and load balancing to TS/RDSH mitigating users
experience degradation due to limited TS/RDSH resources.
C HAPTER 6
Miscellaneous

49
Miscellaneous
Groups
TS/RDSH groups are recommended to be used. This ensures that Published resources are
configured to publish resources from groups. If a new TS/RDSH is to be added, new servers can
simply be added to the group created rather than changing published resources configurations to
be also accessible from new servers.

50
Miscellaneous
Filtering
When configuring Filtering for published resources and selecting User as the filtering type, select
Secure Identifier as the Browse Mode. This is the fastest method that supports group nesting
and renaming.

51
Miscellaneous
Disable Application Monitoring
To save system resources on RDS hosts, it is possible to disable application monitoring if it is not
required.

52
Miscellaneous
Server Reboots
Reboot clears up old sessions and releases resources in use (CPU, RAM, file handles, etc.). It is
recommended to configure scheduled reboots for your TS/RDSH (applicable for frequent logoffs
and logons). This can be carried out in the RAS console by navigating to Farm \ Terminal Servers.
Reboot frequency depends on how heavily the TS/RDSH are utilized.
Hint: Make sure that server rebooting does not cause any downtime. This can be carried out by
offloading users onto other servers prior to reboot by enabling the drain mode.

53
Miscellaneous
Backups
Parallels recommends setting up recurrent backups of Parallels RAS farm settings. This can be
accomplished using Parallels RAS PowerShell, which is a part of Parallels Remote Application
Server beginning with version 15.5.2. Parallels RAS PowerShell is installed by default when you
install Parallels RAS. If you chose not to install it, please run the Parallels RAS installer again and
install the Parallels RAS PowerShell component.
The following sample PowerShell script shows how to export Parallels RAS farm settings to a file.
#Get the current datetime to be used as a name for the backup file.
#You can use any other unique name format that you like.
$Date = Get-Date -Format yyyy.MM.dd.mm.ss
#Import the Parallels RAS PowerShell module.
Import-Module PSAdmin
#Create a Parallels RAS session.
#Since the password must be passed as SecureString, we need to convert it first.
#In your own script, replace "secret" with your Parallels RAS password.
$Pass = "secret" | ConvertTo-SecureString -AsPlainText -Force
#We can now create a Parallels RAS session.
#Replace "user" and "server.company.dom" with your RAS user and server names.
#If executing the script locally, you can omit the -Server parameter.
New-RASSession -Username "user" -Password $Pass -Server "server.company.dom"
#Export farm settings to a file.
#You can specify a different folder for saving the file if you wish.
#.dat2 is the default extension Parallels RAS uses for backup files.
Invoke-ExportSettings $env:userprofile\$Date.dat2
#Close the current RAS session.
Remove-RASSession
Save the above sample script to a file with the ".ps1" extension. To test the script, you can execute
it in the PowerShell console. To execute the script on a schedule, do the following:
1 Open Windows Scheduler and click Create Task.
2 On the General tab page of the Create Task dialog, fill in all required fields.
3 Select the Actions tab page and then click the New button.
4 In the New Action dialog, make sure Start a program is selected in the Action drop-down list,
then click Browse and select your .ps1 script file.
5 Click OK in the New Action dialog.
6 Select the Triggers tab page and click New.
7 In the New Trigger dialog, specify the desired schedule settings.
8 Click OK to close all dialogs.
To import the settings from a saved file into a Parallels RAS farm:
54
Miscellaneous
• In the Parallels RAS Console, navigate to Administration \ Backup and click Import. Specify
the ".dat2" file to import the farm settings from.
• Using Parallels RAS PowerShell, execute the Invoke-ImportSettings cmdlet passing the
path and filename of the backup file.
The complete Parallels RAS PowerShell documentation can be viewed and downloaded from
http://www.parallels.com/products/ras/resources/
Large File Upload / Download via Drive
Redirection
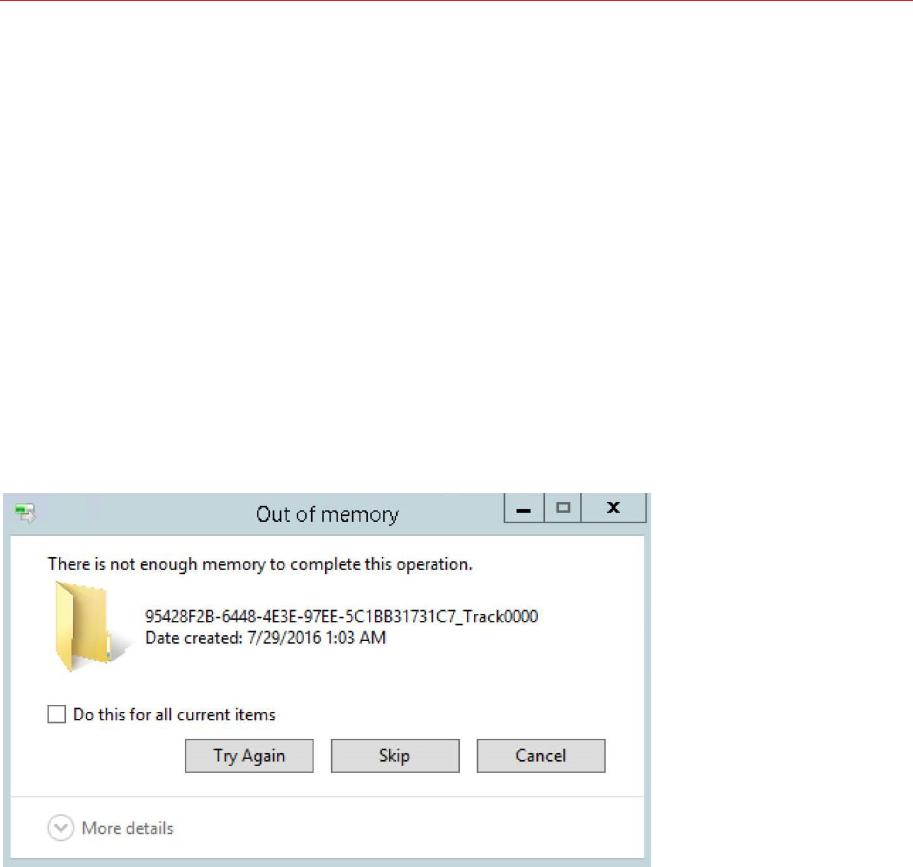
In some cases bandwidth and other factors can cause a memory error when transferring large files
between remote applications and local drives.
For large file transfer optimization, the following settings should be made on both the server and
client side.
RDS/TS Server Settings
Referencing the Remote Desktop/Terminal Server Performance Settings section at the
beginning of this document:
• Set Visual Effects to "Best Performance".
• Set the Windows Paging file to three times the physical RAM.
Disable Desktop Composition under Group Policy (on Windows 2008 R2 only).

55
Miscellaneous
Under Local Computer Policy > Computer Configurations > Administrative Templates > Windows
Components > Remote Desktop Services > Remote Desktop Session Host > Remote Session
Environment, set Desktop Composition to "Not Configured."
Client Settings
Client settings can be changed on a per client basis using Connection Properties or centrally from
the Parallels RAS management console using Policies.
1 For an individual client, under Connection Properties, go the Experience tab and set the
Connection Optimization to WAN (10 Mbps or higher with high latency):

56
Miscellaneous
2 To change this setting centrally for multiple clients, in the Parallels RAS Console, select the
Policies category. Add a policy for a group of users and under Connection Properties >
Experience, set the Experience Optimization to WAN.
Remove Gateway Browsing from Your LAN
Keep your gateway private on your local LAN:
1 In the Parallels RAS console under Farm select Gateways.
2 Open the gateway properties for each Gateway Server in your Farm.
3 Under the Network tab, uncheck "Broadcast RAS Secure Client Gateway Address"

57
Miscellaneous
4 Click OK and then Apply Settings.
Remove Self-Signed Certificate Error
Parallels Remote Application server comes pre-configured with a self-signed certificate to enable
SSL access to the Farm during the testing phase. Self-signed certificates will generate a warning
that the connection is not secure/private. For production purposes, certificates should be
purchased from a Certificate Authority.
During the testing phase you may wish to suppress the self-signed certificate error which can be
done using RAS Policy settings. Note that this policy only works with Parallels Client for Windows,
Mac, and Linux.
To remove the certificate error simply follow the steps below:
1 Navigate to Policies from within the RAS Console.
2 Click
to add a Local/Domain group which will be affected by this policy.
3 Select "Options" under Policy.

58
Miscellaneous
4 Then click on the "Advanced Settings" tab.
5 Check the option "Do not warn if server certificate is not valid".

59
Miscellaneous
6 Click OK and then Apply Settings.

60
Miscellaneous
Remote PCs
Physical PCs can be accessed remotely using the RAS infrastructure:
• Parallels RAS Remote PC agents are used to publish both Applications and Desktops from the
Windows Desktop OS.
• Desktop Operating Systems can only support 1 remote user at a time.
Supported Desktop operating systems:
• Windows 10 Pro, Windows 10 Enterprise, Windows 10 Education, Windows 8.1 Pro, Windows
8.1 Enterprise, Windows 8 Enterprise, Windows 8 Pro, Windows 7 Professional, Windows 7
Enterprise, Windows 7 Ultimate, Windows Vista Business, Windows Vista Ultimate, Windows
Vista Enterprise, Windows XP Professional.

61
Miscellaneous
Configure RemoteFX (Windows 7 and later) using the RemoteFX Settings for Windows
Workstations Runnings Remote PC agents and VDI Agents (p. 23) in the RemoteFX section of
this guide.
VDI
Parallels RAS supports the following VDI hosts:
• Hyper-V & Hyper-V Failover Cluster
• Windows 2008 R2 – Windows 2012 R2 Standard, System Center and Data Center
• VMware vSphere ESX 5.1 – 6.0
• vCenter for Windows v5.1 – 6.0. The vCenter appliance is not currently supported.
• Citrix Xenserver to 6.5
Parallels RAS Agents currently support a max of 1000 VM’s per agent.
The following Windows Desktop OS’s are supported VM’s within the VDI hosts:
• Windows 10 Pro, Windows 10 Enterprise, Windows 10 Education, Windows 8.1 Pro, Windows
8.1 Enterprise, Windows 8 Enterprise, Windows 8 Pro, Windows 7 Professional, Windows 7
Enterprise, Windows 7 Ultimate, Windows Vista Business, Windows Vista Ultimate, Windows
Vista Enterprise, Windows XP Professional.
Configure RemoteFX (Windows 7 and later) using the RemoteFX Settings for Windows
Workstations Runnings Remote PC agents and VDI Agents (p. 23) in the RemoteFX section of
this guide.
VMware vSphere Environments:
• Standalone ESXi Host(s) are supported via the RAS VDI virtual appliance.
• If an ESXi host is managed by vCenter, a RAS agent must be installed on the vCenter server.
With Windows Hyper-V, the Agents are installed on the Hyper-V host.
With Citrix XenServer, the VDI Appliance is used to manage the VM’s on the Citrix Xenserver.

62
Miscellaneous
Examples:
Hyper-V

63
Miscellaneous
VMware using the VDI Appliance

64
Miscellaneous
VMware using vCenter (Windows Only)

65
Miscellaneous
Citrix Xenserver using the VDI Appliance
The Parallels RAS Web Portal uses Windows IIS. This gives the users a friendly web interface to
access their applications and desktops.
The following Windows Servers are supported by the Parallels RAS Webportal.
• Windows Server 2003 Standard Edition, Windows Server 2003 Enterprise Edition, Windows
Server 2003 Datacenter Edition, Windows Server 2008,Standard Edition, Windows Server 2008
Enterprise Edition, Windows 2008 R2, Windows 2008 R2 Enterprise Edition, Window 2008 R2
Datacenter Edition, Windows Server 2012 Standard Edition, Window 2012 R2 Standard
Edition, Window 2012 Datacenter Edition, Windows 2012 R2, Datacenter Edition.
When a user accesses the RAS Web Portal for the first time, they will be prompted to download the
Parallels RAS Client.
• The administrator can assign the Parallels self-extracting client for this process which does not
require full administrative rights on the client system to install.
Parallels RAS Web Portal currently supports the following device platforms:
• Windows, Mac, Linux, Android, iOS, Raspberry PI.
In This Chapter
Windows Prerequisites for Parallels RAS Web Portal ................................................. 66
Configure User Friendly URL ..................................................................................... 67
Windows Prerequisites for Parallels RAS Web
Portal
IIS and .Net are required to be installed under Roles & Features in order to install the Parallels Web
Portal:
C HAPTER 7
Parallels RAS Web Portal

67
Parallels RAS Web Portal
Configure User Friendly URL
By default, clients access the Web Portal via the following URL:
http://<hostname/ip:81>/2XWebPortal/Logon.aspx
To make the Parallels RAS Web Portal more user friendly please do the following.
1 Install the Webportal and pick port 80 instead of port 81.
2 Make sure that port 80 isn’t in use on the server. Common conflicts on Port 80:
• IIS Default Web Site
• Parallels RAS Secure Client Gateway (if installed on this server)

68
Parallels RAS Web Portal
3 Login to ISS manager after you install the RAS Webportal.
4 Change the login URL under Default Documents by adding the document Logon.aspx.
5 Go into basic settings under the site and adjust the physical path to
"C:\inetpub\wwwroot\2xWebPortal"
The Parallels HTML5 Gateway enables clientless remote access to the Remote Application Server
farm from most modern web browsers that support HTML5. The HTML5 Gateway can be
accessed using the following URL:
HTTPS://<Hostname/IP>/RASHTML5Gateway
Currently, the default URL cannot be modified.
Access is delivered through a web access site hosted on the Secure Client Gateway Server.
Multiple Gateway servers can be load-balanced by the High Availability Load Balancer (HALB).
The HML5 Gateway is enabled by default and requires SSL. A self-signed certificate can be used
and is pre-installed with the product. For production, Parallels recommends that an approved SSL
certificate from a Certificate Authority is used.
Due to the clientless nature of the solution, Local drive access from clients is not available.
However, files can be saved on File Shares and on Cloud Drives (Drop Box, Google Drive,
OneDrive, etc.) if those applications are published by the administrator.
Universal printing is supported when using the HTML5 Gateway.
C HAPTER 8
Parallels RAS HTML5 Gateway

Index
A
Active Directory - 6
Active Directory and Infrastructure Services
Considerations - 6
Antivirus Exclusions - 42
Audience - 5
Audio and Video Playback - 30
B
Backups - 51
C
Configure RemoteFX - 21
Configure RemoteFX Adaptive Graphics - 24
Configure RemoteFX Lossless Graphics - 25
Configure User Friendly URL - 66
D
Device and Resource Redirection - 31
DHCP - 11
Disable Administrative Components - 40
Disable Application Monitoring - 50
DNS - 10
E
Enable Audio / Recording Redirection - 27
F
File Services - 11
Filtering - 49
For Windows 2008/R2 - 36
For Windows 2012/R2 - 36
G
General Performance Related Settings - 20
General Purpose RemoteFX Settings - 22
Groups - 49
I
Installation Procedures - 14
Introduction - 5
L
Large File Upload / Download via Drive
Redirection - 53
Load Balancing - 48
Locking Down TS/RDS Host - 38
M
Miscellaneous - 48
P
Parallels RAS HTML5 Gateway - 68
Parallels RAS Web Portal - 65
Printer and Drive Mapping - 44
Printing/Scanning Compression - 45
R
RDP Optimizations - 35
RDP Security - 38
Remote Access Configuration - 18
Remote Desktop/Terminal Server
Performance Settings - 18
Remote FX Settings for Server 2008 R2 - 22
Remote FX USB Redirection - 26
Remote PCs - 59
Remote Session Environment (H.264,
RemoteFX, Adaptive Acceleration) - 32
RemoteFX settings for Server 2012 and 2012
R2 - 23
RemoteFX Settings for Windows
Workstations Running Remote PC Agents
and Guest Agents - 23
Remove Gateway Browsing from Your LAN -
55
Remove Self-Signed Certificate Error - 56
S
Server Reboots - 51
Index

Index
T
Time Zone Redirection - 30
U
Use the Hardware Default Graphics Adapter
for all Remote Desktop Services Sessions -
25
V
VDI - 60
W
Windows 2008 R2 RemoteFX Compatibility -
34
Windows Prerequisites for Parallels RAS Web
Portal - 65
Windows Server Requirements - 14
Windows Server Roles & Features - 15
